Free Barcode Tape Label Creation
http://tapelabels.librelogiciel.com/
Using Google Calendar, Thunderbird and Lighting to full effect
One of the best apps available on Windows is MS Outlook, as a complete suite of apps to organize your life, with Mail, to do lists and a calendar application, which allows for scheduling of meetings, and your time, which will communicate happily with your Windows Mobile or Smartphone Device. Allowing you to know what you are doing while both at your PC or away from it. However, being a commercial application, this can be quite a pricey solution, especially, if your are looking for these features to manage yourself, or maybe just a few others.
However it is possible to archive similar results using Windows, or Linux for free.
Being the owner of an Orange M600 Smartphone, and a Linux user, I spent a long time looking over the Internet, as the best way to get the information shared between my Desktop and my PDA phone. and although there are projects out there , SynCE springs to mind, they are not easy to setup.
So I thought i would look at a different way of resolving the issue.. As always, this is not the only way, its just my way.
Issue
- Cross Platform Calendar Connectivity Windows, Linux, Windows Mobile
- Easy to use
The key to my resolution is Google Calendar, which can be accessed easily enough, especially if you already have a gMail account. If however you don’t have a gMail account, you can create your self a Google Account here, which will give you access to the Calendar functionality. Its pretty self explanatory. Once this is setup, its time to look at your mail client, obviously you could just use google calendar, via the web browser in Windows or Linux, but it doesn’t display to well on a PDA.. Also the aim here, is to emulate some of the functionality of Outlook, which allows you to have access to multiple mail accounts in one location.The Email Client
The software I use is Thunderbird, Its my preferred Mail client, as i use both POP and IMAP based mail accounts, this mail client doesn’t however come with any built in calendar function, which is a reason, so many people berate it, and state that “calendar functionality is required before this app can move forward”. One of Thunderbirds strengths however, is, like its cousin Firefox, it works on a plugin system. That is, people have written third party modules, which can be used to enhance the functionality of Thunderbird. And I use 2 of these pluginfrom has an old version, Try downloading Lightening fromSetup The Plugins
Lightning Plugin for Thunderbird: http://www.mozilla.org/projects/calendar/lightning/
Google Calendar Provider: https://addons.mozilla.org/en-US/thunderbird/addon/4631Quite simply, Lightning provides a calendar interface for Thunderbird, its part of the Mozilla Sunbird project, and helps provide the Schedule interface which standalone Thunderbird is missing.Quote:
Note: The version of the google provider at this time, requires Lightning version 0.7 or higher, and may not work with the one in the Gutsy repository under add/remove, so use the link above to download the latest version.
The magic here, however is the Provider for Google Calendar plugin, which, unlike just adding the necessary links to Thunderbird, to access Google Calendard, not only provides read access, it provides write access as well..Sync the PDA
Install both plugins, and restart Thunderbird, you will then be shown, a Calendar in the left pane, this calendar has 3 tabs Agenda, Todo and Calendars. To setup Google Calendar, click on the Calendar tab.
Click on the New Button, in the Calendar Tab, and you will be given a choice, you need to select, On the Network. Click on Next, there is an option for Google Calendar, select this.
In the Text bar under the Google Calendar you will need to enter the Link URL which allows you to write to your Account, you can find this, buy logging into the Google Calendar account you created earlier.
Create a new Calendar, or if you already have a celedar created, click on the down arrow next to the calendar. And click on Share this Calendar.
You will be taken to a new page, where you will need to click on Calendar Details on the top of this page.
Then Select the XML button, next to the Private Address, this will allow you the read/write access to the calendar, if you need read only access, or wish to share calendards with read only access, use the XML button next to the Public Tab.
When you click on the XML button a URL will be displayed (i’ve edited the whole strin below for security reasons) Copy this URL , and paste it into the Thunderbird Text box, then click on Next.
Give the Calendar a name which you will use in Thunderbird to identify this calendar, and choose a colour, this is the colour which will identify your Google Calendar, if you are using multiple calendars. Then CLick on Next and then Finish.
You will then see your calendar listed as available. you should now be able to add an event in either Thunderbird, or the wEb Interface, and both will update to show the events. You can set reminders, repeat events, and all the usual type of Schedule details.
The next step is to sync the Calendar with the PDA, this is done using the GMobileSync app for Windows Mobile or Smartphones. it requires .NET CF 2.0 which is available for download from the site, and provides not only read access to they Google Calendar, it also provides write access. This means as well as having PDA based access to your existing schedule, you can provide updates from your PDA to your calendar too. The application requires your login ID and password for the Google Calendar site. and works as far as i’m aware over both Wifi and GPRS networks, however i will confess, with UK prices as they are for Data over GPRS i’ve only tried Wifi. The Sync is a manual operation, and not automatic (yet)
Windows XP On Screen Keyboard at Login Screen
Download the OSKGina from Siemens website and waalaaa...
The OSKGina v2.0 can be downloaded from Siemens (and possibly others)
http://support.automation.siemens.com/US/llisapi.dll/csfetch/22402193/OSKGinaSetupV2_01.exe?func=cslib.csFetch&nodeid=22403228Alternative to Microsoft Office
Well i guess the only reputable challenger would be OpenOffice.

The latest release version is Open Office 3.0.
In the new version: native Mac OS X compatibility, support for version 1.2 of the OpenDocument format, and compatibility with Microsoft's OOXML format.
The latter feature is particularly useful, given that Office 2007 saves .docx files by default - something that's confused many a hapless user as they tried to send stuff to people using older versions of the office suite.
Here's the link to it.
Alternative to Microsoft Project
http://open-source-project-management-tools.blogspot.com/
e.g. Open Workbench, TaskJuggler, GanttProject
Open Workbench Screenshot

TaskJuggler Screenshot

GanttProject Screenshot

Recover lost wireless network key
Source Link
"
WirelessKeyView recovers all wireless network keys (WEP/WPA) stored in your computer by the 'Wireless Zero Configuration' service of Windows XP and by the 'WLAN AutoConfig' service of Windows Vista. It allows you to easily save all keys to text/html/xml file, or copy a single key to the clipboard.
"
Google Picasa 3 Beta Release
There are the exciting new features in Google Picasa 3.
 | Sync your Picasa 3 and Picasa Web Albums editsTired of having to manually re-upload your photos after making further edits? By enabling 'Sync to Web,' edits made to your photos in Picasa 3 are automatically transferred to your corresponding online albums. You can sync the following changes:
Getting startedThe Sync to Web button TroubleshootingYou can disable the sync feature at any time by clicking the Sync to Web button again, or by selecting Disable Sync in the drop-down menu to the right of the Share button in the folder or album header. All your photos and their edits up to this point remain online, but any new edits and changes will no longer be synchronized. The following changes don't transfer to your online albums:
|
 | Retouch your imagesAlways want to be airbrushed? Use the Retouch tool to remove unsightly blemishes and improve photo quality. It can also help you to restore old photos with marks, water stains, and scratches to excellent condition. When editing any photo, just click the Retouch button |
 | Preview image files with Picasa Photo ViewerThe photo viewer is a fast, lightweight application for viewing images on your desktop or through Windows Explorer. Installed with Picasa 3, it lets you to take a quick look at images without having to fully open the Picasa 3 program. What you can do with the photo viewer:
From your computer desktop or from within Windows Explorer, just double-click any image file
If you'd prefer to use a different application to view certain file types, deselect the file types that the photo viewer shouldn't open. To disable the Picasa Photo Viewer entirely, click the 'Don't use Picasa Photo Viewer' option. |
 | Make a movieCombine your photos, videos, and music into a movie, and create a Windows Media file. Share it with friends by uploading it directly to YouTube. About the movie maker:
There are two ways to launch the movie creation screen:
|
 | Capture your screenInstantly take and import your screen captures and webcam captures into Picasa 3. Screen capturesPress PrtScn to capture a shot of your entire screen. Ctrl+PrtScn will capture the highlighted window. These images will be placed in the 'Screen captures' folder.
If you're having trouble importing screen captures, make sure Picasa 3 is open. Screen captures won't be imported if the application is closed. Webcam captureThis is webcam importing made simple: Capture video or stills from within Picasa 3, and import them in the same instant. Make sure your webcam is operational, and then click the Webcam Capture button
If the Webcam Capture button is inactive, first make sure your webcam is set to go. Then try closing Picasa 3 and opening it back up. |
 | Add text or watermarks to your photosYou can easily personalize your photos using the Watermark and Text tools. WatermarksHelp protect your images by stamping a watermark on all images that you export or upload. The watermark signature will be placed in the lower right-hand corner. Upload photos with watermarks
Click the Tools menu in Picasa 3, select Options, then click the Web Albums tab. Select the option labeled 'Add a watermark for all uploads.' Type the text for the watermark in the field below the option. Export photos with watermarks
When you click the Export button in the Photo Tray, you can select the 'Add a watermark' checkbox to include a watermark on your exported images. Type the text for the watermark in the field below the option. TextUse the Text tool to add text quickly and easily to your photographs; you can even print the result. You can edit the style, size, color, and alignment of the text, as well as drag it to your desired location on the photo. When editing a photo, click the Text button
The text change isn't permanent. Once you've added your text, you'll see a 'Show Text' checkbox on the 'Basic Fixes' tab for that image. Deselect the checkbox and the text will disappear. |
 | Print captionsYour captions are about to see a little more action. You can now print your captions or photo file names on or below your photos. Control the style and color of your printed caption, in addition to the width and color of the printed photo border. After you've selected the photos you'd like to print, click the Print button in the Photo Tray. Click the Border and Text Options button |
 | Upload easily to Picasa Web AlbumsUse the Drop Box to hold quick uploads and upload throttling to multi-task during your upload. Drop-box uploadThe Drop Box is an online album that serves as a holding pen for your quick uploads. Click the Upload to your Web Albums DropBox button Upload throttlingYou can choose to have Picasa 3 reserve some of your Internet bandwidth for surfing the Web while you're doing large uploads to Picasa Web Albums. During your upload, the dialog box will have an option labeled 'Don't eat all my bandwidth.' Just select this checkbox, and then continue multi-tasking. |
 | Control your Picasa Web Albums settingsIf you have an online album in Picasa Web Albums, you can now control the online settings through the corresponding folder or album in Picasa 3. There are a few different controls located in the drop-down menu
Troubleshooting
|
 | Manage folders on your computerIt's now possible to move entire folders around on your hard drive from within Picasa 3. From the folder list, right-click the folder you'd like to move, and select Move folder. Choose your desired destination or create a new folder altogether.
These moves are permanent on your hard drive, so make sure you properly stow your folders. |
 | Get more information about your photosWe've added new icons and tools to the Library view to quickly communicate useful information about your photos. |
Screamer Radio

Looking for a small in size and with recording capable internet radio player?
I recommend 'Screamer Radio'. It's lightweight and low in resources.
Hit the link below to take a look yourself. :)
http://www.screamer-radio.com/
T r u e C r y p t - Free open-source disk encryption
Source Link: http://www.truecrypt.org/
Main Features:
- Creates a virtual encrypted disk within a file and mounts it as a real disk.
- Encrypts an entire partition or storage device such as USB flash drive or hard drive.
- Encrypts a partition or drive where Windows is installed (pre-boot authentication).
- Encryption is automatic, real-time (on-the-fly) and transparent.
- Provides two levels of plausible deniability, in case an adversary forces you to reveal the password:
1) Hidden volume (steganography) and hidden operating system.
2) No TrueCrypt volume can be identified (volumes cannot be distinguished from random data).
- Encryption algorithms: AES-256, Serpent, and Twofish. Mode of operation: XTS.
Further information regarding features of the software may be found in the documentation.
Resize HTML Forms In Firefox
Article Source Link
"
Some web developers like to squeeze small html forms into their websites which are uncomfortable to use for the visitors of the website. Imagine a comment form that displays three lines that each can take only a few words. It’s problematic to write a comment of a hundred words or so in that box and nearly impossible to proofread it once you are done.
Text Area Resizer And Mover comes to the rescue; At least for Firefox users. The Firefox extension makes it possible to resize virtually any html form on the Internet. This is done in an uncomplicated manner.
Once a html form has been located that the user wants to resize he simply presses the right-mouse button after moving the mouse into the form. The mouse pointer changes to a resize symbol and the html form can be resized by moving the mouse.
The default html form at Ghacks for commenting on an article:
The altered html form at Ghacks:
It is possible to make it smaller or bigger although most users will probably stick with the latter. Text Area html forms are those that usually span across multiple rows. The extension cannot be used to increase the size of the Google Search form but as you can see in the images above it is possible to change comment forms and the like easily.
The forms only expand to the right and bottom of the screen but never to the left or upwards.
"
How to build and customize your own PBX with Asterisk
Article Source
"
This article demonstrates how easy it is to roll your own PBX in about an hour or two. Provided that the instructions herein are followed carefully, you too should be able to set up your very own switchboard/PBX system and all for the cost of the target hardware of your choice.
What is a PBX and why set one up?
A PBX or “Private Branch Exchange” is like a miniature phone company/switch in your own office/house. The PBX is responsible for making sure calls are routed properly. Situation: when Joe wants to dial Suzy in the office down the hall or downstairs in the TV room, he just picks up the phone in his room/office and dials a local extension just a few digits long. If he wants to call someone across town or around the world, he dials an “outside line” prefix (usually a 9) plus the desired number and the PBX routes his call to the PSTN (Public Switched Telephone Network) just like any other dialed call. Also, if Joe has four teenaged kids, instead of answering their calls and acting as the house receptionist, he can just setup a menu that allows callers to dial the person they want and then needs not be disturbed.
Most people are familiar with PBXs because they’ve used them in an office environment, but what if you wanted to use one in your house? Enter Asterisk.
The beauty of Asterisk (Asterisk.org) is that it is free and offers all this functionality right out of the box. Asterisk is a software implementation of a hardware PBX and can run on a variety of hardware platforms. The features and benefits of owning an Asterisk PBX are numerous, and seemingly only limited by the imagination of the person who sets up and uses an Asterisk PBX. Listed on the project page are just some of the many features that can be implemented. I encourage anyone to explore these features as it will give you some idea for setting up your system in a way that makes it more than worth your while.
Prepare for setting up your PBX
There are many ways of setting up an Asterisk PBX, with some being easier than others. The easiest manner in which to set up a fully functional Asterisk PBX is to download and install a precompiled/tuned distribution such as Trixbox, PBX in a flash, Asterisk NOW, etc. Just take your pick of those. These are great if you don’t care to learn about how your PBX operates or need to do a mindless “click and drool” install. The problem with precompiled asterisk distributions is, while they are simple, they are not as flexible and extensible as a home-brewed Asterisk installation from the source code. When you install one of these “distros”, it is quite often that important decisions are already made for you, and you must work within the framework of the distribution to keep the box “happy”. When you roll your own Asterisk from the sources, you get more say in what goes into the build and how it is customized/extended at the expense of a slightly more complicated planning and installation process. However, it’s not as hard as you might think and it’s quite worth it in the end to “roll your own”.
Asterisk installed from the source code enables you to pick your choice of underlying OS (Debian, Ubuntu, Fedora, Mandrake, SuSE, etc) and also fine tune the installation for your OS environment and your hardware for best possible performance. In this article I will cover the steps needed to install Asterisk for the Ubuntu Linux operating system. This article assumes you know how to do a minimal command line only base system install of Ubuntu Linux. You certainly don’t want to run a GUI on your Asterisk box as it would consume unnecessary resources.
Step 1: prepare a minimal Ubuntu machine, wiht a command line only install
Step 2: download source packages
After you’ve prepared your minimal Ubuntu machine, you will need to download a few source packages from Digium (the maker of Asterisk). Please perform the following steps on your command line as the root user. (NOTE: on Ubuntu systems, the root account password needs to be set in order to login as root) To set your root password, log in as your regular user account you created during installation and type the following commands:
sudo passwd root
when asked for your password enter your regular USER password, hit ENTER, followed by the desired root password and then hit ENTER, confirm the desired password once more and then you’re done.
Logged in as the root user we’ll download the needed packages by running the following script in your terminal screen. If you are familiar with Putty, you can also do this remotely via a windows desktop or SSH into the box as root from any other Linux/Mac machine.
NOTE: we will be using Asterisk 1.4 NOT 1.6 as 1.6 is the unstable release.
Source packages needed from Digium:
asterisk-1.4.21.2
zaptel-1.4.11
libpri-1.4.5
asterisk-addons-1.4.7
asterisk-gui
I have written a script file to simplify the process on an Ubuntu 8.04 system. Copy and paste the following code into a new file in a terminal window and save the file as “astsetup.sh”. Then when you save the file, make it executable by running this command: chmod +x astsetup.sh.
——> BEGIN COPYING CODE TO NEW FILE
######## Prepare Build Environment
apt-get install build-essential speex libspeex-dev gsm-utils \
libgsm1-dev libgsmme-dev libgsm1 libgsm-tools \
libncurses5-dev ncurses-term linux-headers-2.6.24-19-generic \
libncurses5-dbg doxygen subversion
######## Download Digium (Asterisk) Source Packages
wget http://downloads.digium.com/pub/asterisk/releases/asterisk-1.4.21.2.tar.gz
wget http://downloads.digium.com/pub/zaptel/releases/zaptel-1.4.11.tar.gz
wget http://downloads.digium.com/pub/libpri/releases/libpri-1.4.5.tar.gz
wget http://downloads.digium.com/pub/asterisk/releases/asterisk-addons-1.4.7.tar.gz
svn co http://svn.digium.com/svn/asterisk-gui/trunk asterisk-gui
######## Extract all packages for building
tar -zxvf asterisk-1.4.21.2.tar.gz && tar -zxvf zaptel-1.4.11.tar.gz \
&& tar -zxvf asterisk-addons-1.4.7.tar.gz && tar -zxvf libpri-1.4.5.tar.gz
######## Begin Building and Installing Source Packages
cd libpri-1.4.5
make
make install
cd ../zaptel-1.4.11
make clean
./configure
make menuselect
make install
make config
cd ../asterisk-1.4.21.2
make clean
./configure
make menuselect
make install
make samples
make progdocs
cd ../asterisk-addons-1.4.7
make clean
./configure
make menuselect
make install
make samples
cd ../asterisk-gui
./configure
make
make install
make samples
cd /root
mkdir packages
mv *.gz /root/packages/.
echo INSTALLATION COMPLETE PLEASE CONFIGURE WEB GUI
———-> END COPYING CODE TO NEW FILE
One final step remains in order to bring the GUI up and running. We must edit two files:
/etc/asterisk/http.conf and
etc/asterisk/manager.conf.
/etc/asterisk/http.conf:
[general]
enabled=yes
enablestatic=yes ; without this, you can only send AMI commands, not display
; html content
bindaddr=0.0.0.0 ; address you want the Asterisk HTTP server to respond on
bindport=9000 ; port you want the Asterisk HTTP server to respond on
prefix=asterisk ; will form part of the URI, similar to a directory name
/etc/asterisk/manager.conf:
[general]
enabled=yes ; you may already have AMI enabled if you are using it for other things
webenabled=yes ; this enables the interaction between the Asterisk web server and AMI
[admin] ; This is the manager username. You can name the user whatever you want
secret = password
read = system,call,log,verbose,command,agent,user,config
write = system,call,log,verbose,command,agent,user,config
———–
That’s it! Restart your PBX server and point your browser to:
http://ip-of-pbx:9000/asterisk/static/config/cfgbasic.html (where IP of PBX is the IP address of your PBX box)
You should then see the web GUI and should be able to logon and start creating extensions (users).
If you don’t see the GUI after restarting your PBX, login as root and just start Asterisk by typing asterisk on the command line. You can also set it to start at system boot by adding it to your /etc/rc.local startup script. Also, if you have an account with a VOIP service provider, you can setup your PBX to be the “gateway” to your office/home with ease.
Asterisk is very flexible, scalable, and limitless in its scope of use, so there is no way I can tell you everything that can be done with this amazing piece of software. It’s use is not just limited to communication and phone management and there are thousands of hacks that can be applied to Asterisk. Some of them are:
- Home Automation using X10 addressable switches
- Remote home/office alarm/lock control
- Remote environmental/audio monitoring
- Conference Rooms
- E-mail reader (text to speech access to any email account)
- Remote Dictation
- Voice Recognition
- Ability to run system commands by phone - Remote Control
Additional Materials
Because of the power and limitless flexibility of Asterisk, there is no available text that comes close to covering the broad scope of this software. The best guide I can recommend is the O’Reilly self-titled book “Asterisk”. That is a good step to begin to understand much of the power available to this platform. I would suggest this as the first guide to begin to learn additional features.
Phones and Extension Types
Asterisk supports any standards based SIP or IAX compatible voip phone. One of the best well known suppliers is www.voipsupply.com and they sell a wide range of voip phones that work with asterisk. Softphones and VOIP ATAs (Analog Telephone Adaptors) are also another way to interface with your Asterisk system. With an ATA you can turn your existing analog corded or cordless phones into VOIP phones. I have an old Western Electric Model 302 from the late 1920s that is now setup as a voip extension and it is a ROTARY phone! NOTE: Not all voip ata units understand pulse dialing, so be sure before you buy if you intend to use a rotary phone for nostalgic purposes. Good deals for voip phones and voip ATAs can be had online at various sites, but don’t overlook the possibilities that may exist at your local swapfest. Near where I live, MIT holds a swapfest during the summer season on the 3rd Sunday of the month and I’ve scored some real bargains there! Look for swapfests in your area, or even check Craig’s List.
Voip Service Providers/PSTN
Asterisk can connect with the world either directly with a voip service provider that allows a “byod” (Bring Your Own Device) plan, or directly with the PSTN (Public Switched Telephone Network) via a Digium interface card. The Digium card is not required to interface with a voip provider over the internet though. Some voip providers that welcome Asterisk (and other devices) are: Broadvoice and Teliax. If you want to interface with Ma Bell, you might be interested in Digium’s line of cards. These can interface with standard POTS PSTN lines and provide outbound calling from extensions on your Asterisk system. Most of these cards feature built-in echo cancellation for best call quality. If you’re a business user, you can connect Asterisk to a T1/E1 or PRI digital telco offering via their digital cards.
Community Support
Asterisk is supported by Digium and the Asterisk Open Source community. There are numerous resources available for the taking on the internet that allow you to extend the flexibility and functionality of your Asterisk PBX. www.voip-info.org is one of many public voip forums where a wealth of information is available. Available resources can be anything from example configurations, scripts, feature enhancements, function modules, advice, and troubleshooting.
The intended purpose of this feature was to simplify a nice and lean sourcecode installation of Asterisk onto a pupular Ubuntu (or any other Linux) host system and to ease the new user or experimenter in wading into a huge pool of possibilities that are only limited by the imagination of the user. The door is open, just take your step through!
"
How to view Windows ACL - Part 2
DumpSec v2.8.6
"
Freeware. It dumps the permissions (DACLs) and audit settings (SACLs) for the file system, registry, printers and shares in a concise, readable listbox format, so that holes in system security are readily apparent. DumpSec also dumps user, group and replication information. Platforms: Windows NT"
I'm using this free utility and it really saves me a great deal of time. :)
How to view Windows ACL
Here comes the savior and time saver tips.
Article Source
"
Takeaway: Changing the permissions on files or folders for multiple users and groups can be a major administrative nuisance. Luckily, the Windows command-line tool Cacls.exe can help, especially when used in batch files.
Cacls.exe is a Windows NT/2000/XP command-line tool you can use to assign, display, or modify ACLs (access control lists) to files or folders. Cacls is an interactive tool, and since it's a command-line utility, you can also use it in batch files. I first used Cacls in a batch file as part of a new user creation process and found it quite useful. You can also use Cacls in conjunction with other command-line tools. Used with other administration tools, Cacls will make it much easier to handle administrative tasks performed in large environments.
As a companion to this article, I created a Cacls reference guide you can download. It contains explanations of parameters, related resource links, and usage scenarios.
Working with Cacls
The usage of Cacls is from the command line for single tasks or within a batch file for multiple operations. The default location of Cacls.exe is in the %SystemRoot%\System32 folder for all installations of Windows NT, 2000, and XP and requires the NTFS file system.
Cacls usage is similar across all Windows versions, which eases the learning curve across new releases of Windows. To see the Cacls options, start a command prompt, and type cacls. This will show a list of options and parameters. The simplest operation that Cacls can perform is to display the ACLs of a file or folder with a command such as:
cacls c:\folder\file.txt
Cacls also allows for the use of wildcards, variables, and multiple permissions or users per line. Cacls' rich feature set gives you some powerful configuration options. Table A shows the operations Cacls can perform, along with the corresponding option flags.
| Operation | Parameter |
| Change ACLs of specified files in current folder and all subfolders | /T |
| Edit ACL instead of replacing it | /E |
| Continue on access-denied errors | /C |
| Grant specified user access rights; Permissions are Read (R), Write (W), Change (C), Full Control (F) | /G user:perm |
| Revoke ACLs | /R user |
| Replace specified user’s access rights; Permissions are None (N) and same options from grant operation | /P user:perm |
| Deny specified user access | /D user |
Windows 2000 and XP also provide three new descriptive display objects to the Cacls listing. These describe the inheritance attributes of Active Directory objects. For example, Figure A shows the results of the command cacls C:\xfer\user-1. This displays the ACLs for this sample user directory.
| Figure A |
As you can see, the three inherited objects that are displayed are:
- CI—Container inherit
- OI—Object inherit
- IO—Inherit only
Using Cacls in batch files
One of Cacls' administrative benefits is that you can pass it %1 variables when used in batch files. This can make Cacls an integral part of a large user administration process. To highlight this feature, let's run through an example that will perform the following:
- Display the ACLs for a folder and its subfolders
- Grant a Change/Write ACL for the primary user of the folder and a Read ACL for another user
- Revoke an ACL for a different user to the same folder
The bat file (test-variable-pass.bat) will look like this:
echo This is C:\test-variable-pass.bat
echo Test of variable passing in Cacls
cacls %1 /t
cacls %1 /e /g user-1:W user-2:R
cacls %1 /e /r user-3
From the command prompt, I ran:
C:\test-variable-pass c:\xfer\user-1
For a fancier situation, I could put a> c:\dump.txt at the end of the command prompt entry to pipe the results to a text file for review later. This is handy for searches on large operations. Of course, the %1 variable is not the only variable I could specify for use with this bat file. You can use any number of variables.
Limitations and workarounds
Cacls is a powerful tool for administering your ACLs, but you should be aware of a few quirks. Let’s take a look at some of these situations.
Answering the Y/N prompts automatically
When using the grant (/g) option, Cacls does not provide a way to answer Y or N within the parameters. The workaround is to use the resource kit tool XCacls (explained in the Cacls reference sheet available for download), which has an option to bypass the confirmation prompt. Another option is to place an echo y| or echo n before the Cacls command requiring the Y/N within your bat file.
Cacls (and XCacls) should be local
You can run Cacls from one computer to another, but it may not always work. A better practice is to perform Cacls operations at the computer in question or through a terminal service. For example, I can run a Cacls grant (/g) command from one computer to a resource on a remote computer over the network, and it will accept the ACL entry for a nonexistent account without error. Figure B shows where the 2kas.txt ACLs are displayed before and after the remote Cacls execution. (Notice the Account Domain not found message.)
| Figure B |
Special file access right assignments
The Cacls tool limits ACL assignments to Read, Write and Change (which are the same), Full Control, or None. The special rights are: change permissions, take ownership, execute, and delete. These aren't available with Cacls, but the XCacls tool can address this limitation.
Current folder and subfolders
When using the option /t, be prepared to wait. As you may be used to from the Windows NT GUI, rewriting the ACLs in Windows Explorer using the Replace Permissions On Subdirectories option can take a while. Windows 2000 and newer Windows versions support an automatic propagation of inheritable Access Control Entries (ACEs). But if you use Cacls with the /t option, recursion will occur and it will take some time.
Open or locked files
Cacls cannot display or modify the ACL state of files locked in exclusive use.
Be careful
If you are giving Cacls or XCacls a test drive, beware that you may lock users or yourself out of a file, folder, or drive. Thus, thorough testing and experimenting on a test network system is a good idea.
Summary
Cacls is a powerful tool that can help manage your ACLs. You can also use it in batch files, which is particularly useful in large environments. Utilizing Cacls or XCacls in conjunction with other Windows administration tools can make management of large numbers of user accounts much easier.
"
Free and Robust Inventory / Asset Software
As the list of features is too many, i'm not going to list them all out here.
Do check out the respective sites for the features. :P
Do update me if you have any good recommendation as well!
Here are some of the great softwares that i found:
1) Open-AudIT

2) OCS Inventory NG

3) GLPI

HOWTO: Exclude your visits from Google Analytics
Often i find the Google Analytics not able to differentiate my visit with real visitors. After surfing around, i finally found the solution.
Article Source Link"
Introduction
In my view, one of the minuses of Google Analytics (GA) is the difficulty of excluding our own traffic (aka internal traffic) from the reports. As per this help article, there are two methods of achieving this. One is to set up a filter to exclude traffic from a given IP address or a range of addresses. This method is undesirable if you are using a connection that assigns dynamic addresses for each session.The other method is to filter using a cookie installed in your browser. This method is more reliable and safer than using the first method. But the caveat is installing the cookie as it is not straight forward. And the second method described in the help page is flawed according to this discussion.
The Steps
Here are the tried and tested steps to exclude your traffic from GA.1) Open your template in the Edit HTML mode and scroll right to the end where your tracking code is installed. Locate the script shown below and add the line shown in red.
Replace the variable passed to the _setVar() function with something applicable to you. The string you provide here ("exclude_ids_bguide" in this case) is called the filter pattern and it will be used later when we create the filter.
2) Save the template and visit your blog from all the browsers that you want this cookie installed. For example, if you are using Firefox and IE, visit your blog's homepage from both the browsers. If the page is already loaded, make sure that you do a page refresh.
The next step is VERY IMPORTANT!
3) Go back immediately and remove the line added (i.e. the line shown in red) in step (1), from your blog template and save it again. If you leave this line, all visitors to your blog will also get the cookie installed and you will not have any visits. That's the danger here. Make sure that you remove it immediately after step (2)
4) Login to GA and create a Custom Filter for this cookie. Provide the values as shown in the figure below and select the profile (i.e. your blog address) that you want to exclude. Make sure that you copy the exact filter pattern that you gave in step (1) above.

You will have to wait about a day until you confirm that your visits are now excluded.
"
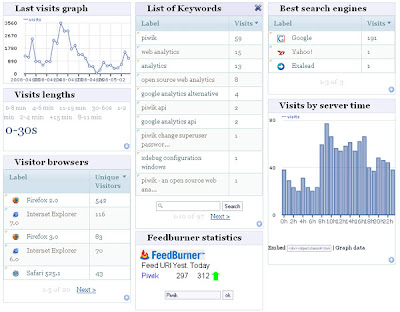
Open Source Google Analytics Alternative
Article Source Link
"
 Google Analytics may be free, but it is still based on proprietary technology - which means you only ever get reports on the things that Google thinks are necessary and some of those reports are aimed at people using Google's other services (managing campaigns on AdWords, for example). Further, using Google Analytics means that you're tied to Google's TOS. Enter Piwik, which aims to be an open source alternative to Google Analytics. It is closely affiliated with OpenX, the open source ad server alternative to Google Ad Manager [Ed: which we just started using on RWW].
Google Analytics may be free, but it is still based on proprietary technology - which means you only ever get reports on the things that Google thinks are necessary and some of those reports are aimed at people using Google's other services (managing campaigns on AdWords, for example). Further, using Google Analytics means that you're tied to Google's TOS. Enter Piwik, which aims to be an open source alternative to Google Analytics. It is closely affiliated with OpenX, the open source ad server alternative to Google Ad Manager [Ed: which we just started using on RWW].
While OpenX has been around a while and has good traction, Piwik is fairly new and under the radar. It surfaced first as PHPMyVisites and is only at version 0.1.5, which is a sign that it is still for the highly committed.
Piwik originates from France and almost all the attention so far has been from outside USA. It seems to be catching on in Japan and China, as well as in Europe. The team responsible for Piwik seems to be made up of interns from big companies such as Amazon, Intel and even Google.
You need PHP and MySQL to use Piwik, which is no problem for techies but any widespread adoption will need a hosted version. Some entrepreneur is likely to offer that. Plug-ins to WordPress and other blogging platforms will also be needed, but cannot be that hard.
Open source products usually get traction, even when they are raw, when the alternative is too expensive or restrictive. Google Analytics is free, so it is hard to see rapid adoption by bloggers and small media companies. It is possible that Piwik will get better traction in companies that already use one of the expensive web analytics services from companies such as Coremetrics, Omniture and Visual Sciences/Websidestory.
Larger companies may have some pause for concern before switching to Google Analytics, because of the service's Terms of Service. An analyst in the IT department is likely to point out two clauses (yes big companies DO read this stuff):
"2. FEES AND SERVICES . Subject to Section 15 herein, the Service is provided without charge to You for up to 5 million pageviews per month per account, and if You have an active Adwords campaign in good standing, the Service is provided without charge to You without a pageview limitation.
Google may change its fees and payment policies for the Service from time to time including but not limited to the addition of costs for geographic data, the importing of cost data from search engines, or other fees charged to Google or its wholly-owned subsidiaries by 3rd party vendors for the inclusion of data in the Service reports."
So, don't go above 5 million page views without paying something to Google via AdWords. That may make one a bit uneasy, but it is the "Google may change its fees and payment policies" that will have both IT and Legal aiming to nix the deal.
Then a bit later on you get:
"6. INFORMATION RIGHTS AND PUBLICITY . Google and its wholly owned subsidiaries may retain and use, subject to the terms of its Privacy Policy (located at http://www.google.com/privacy.html , or such other URL as Google may provide from time to time), information collected in Your use of the Service. Google will not share information associated with You or your Site with any third parties unless Google (i) has Your consent; (ii) concludes that it is required by law or has a good faith belief that access, preservation or disclosure of such information is reasonably necessary to protect the rights, property or safety of Google, its users or the public; or (iii) provides such information in certain limited circumstances to third parties to carry out tasks on Google's behalf (e.g., billing or data storage) with strict restrictions that prevent the data from being used or shared except as directed by Google . When this is done, it is subject to agreements that oblige those parties to process such information only on Google's instructions and in compliance with this Agreement and appropriate confidentiality and security measures."
In short, they have the right to use your data. We have lived for a long time in a world where Microsoft and others charged for the software and kept it under a tight IP control, but did not try to take any use of the data. Google reversed that. Google is happy to let you use anything for free, as long as they get to use your data. That is OK for most individuals and small businesses, but totally unacceptable for large companies.
Piwik is working hard to be developer-friendly, not just relying on open source. They claim 4 big advantages:
- Open API
- Plug in architecture
- Data abstraction layer
- Customizable dashboard
But the nub of the issue for most big companies will be the data ownership issue. That is why Piwik is really a Google Analytics alternative, even if they will see few firms switching from GA initially. IT groups, under pressure to cut costs, will look at Google Analytics as an alternative to their current analytics software and reject the option based on TOS restrictions. Then some bright spark will Google the term "open source alternative google analytics" and see Piwik on top of the organic listings.
"
Firefox 3 and Java
Try the below steps to resolve it:
1) Go to Control Panel
2) Double click on 'JAVA'
3) Click on 'Delete Files'
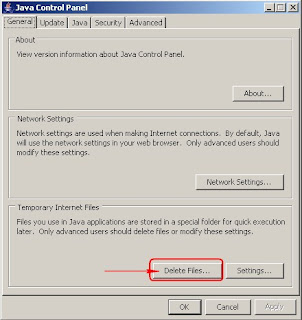
4) Click 'OK'.
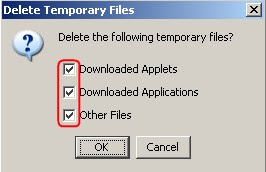
5) Restart 'Firefox' and try again.
Do update me if it's not working for you. :)
How to remove AVG 8.0 Link Scanner
Create a shortcut of the installation file. Then edit the shortcut to run with the parameter below:
# Run the installation with the parameters :
/REMOVE_FEATURE fea_AVG_SafeSurf /REMOVE_FEATURE fea_AVG_SafeSearch
> AVG 8.0 Free SCREENSHOT BEFORE LinkScanner removed:
> AVG 8.0 Free SCREENSHOT Without LinkScanner:
Foxit Reader 2.3: How to Disable Ads
Article Source Link
"
By default, the free version of Foxit Reader has six ads. In earlier versions of Foxit, you could disable the ads simply by clicking on each one. This practice no longer works but you can prevent them from appearing again by creating and executing a simple reg file.
1. Open Notepad.
2. Copy and paste the following into the new text document:
[HKEY_CURRENT_USER\Software\Foxit Software\Foxit Reader\MainFrame]
"ShowEditorAd_908"="0"
"ShowReaderAd_908"="0"
"ShowTypewriterAd_908"="0"
"ShowPOAd_908"="0"
"ShowSDKAd_908"="0"
"ShowFFAd_908"="0"
3. Save the document as foxit_noads.reg.
4. Merge the new file into the registry by doubler-clicking it.
5. If you're using Windows Vista, continue through the UAC prompt and confirm that you wish to perform the action.
"
Remove PDF Document Restrictions
This wonderful free software or freeware unlocks your lock PDF. Isn't this great? :)
"PDF Documents can be protected by the creator by disabling specific functions in the PDF reader. Some options are for example to prevent printing, copying or editing of documents. One way around those restrictions would be to make simple screenshots and print those screenshots if printing would be disabled. This however is not the best way and there is actually a solution that can remove PDF document restrictions easily.
PDF Unlocker (via Techtrends) is a free software that can unlock PDF Document restrictions. This is done by moving the pdf document on the shortcut of PDF Unlocker which will remove the restrictions automatically and create a new pdf document without the restrictions.
This pdf document can be printed, edited and copied. PDF Unlocker has a second function. PDF Documents can be password protected to prevent unauthorized access to them. The software provides a way to unlock the pdf document if the user can provide the password that protects it."






 in the folder or album header.
in the folder or album header.